Pull-Through Identity Modeling: One Identity to Rule Them All

I’ve worked on a lot of Identity and Access Management (IAM) projects over the years. The goal is always to centralize the IAM infrastructure. This is due to a lot reasons around Security, Experience, and enforcement of organizational standards. I’ve had a lot of success doing this and saw organizations and users benefit from the […]
Identity Governance and Newton’s Laws of Motion
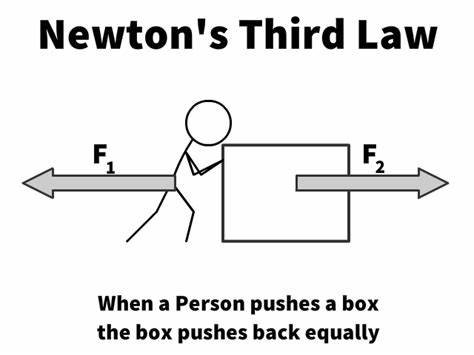
Identity and Access Management (IAM) is complex. When I’m working with customers, you can get lost quickly when trying to describe all the different capabilities and functions of IAM. Especially when you start talking about Identity Governance (IGA) and all the connected applications, it can become a bit unwieldly. Given I always try to keep […]
Can I Integrate My API Gateway with My Authentication Provider…..
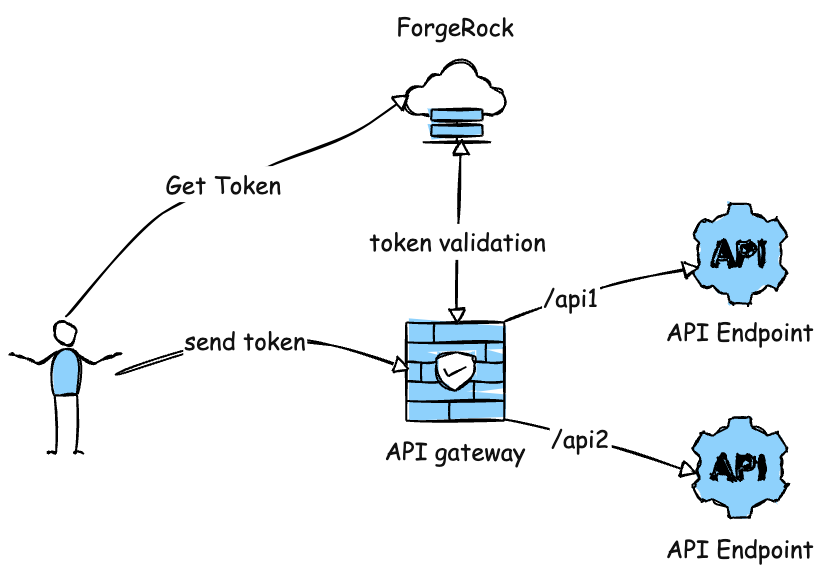
Integrating disparate cloud infrastructure and authentication providers can be done. This post looks at integrating Oracle OCI API Gateway with ForgeRock Identity Cloud.
Which vendor IAM Solution is Best?

I do a lot of general advisory work and calls with customers, partners, colleagues and commonly am asked the direct questions: What is the best vendor for my IAM program (insert IGA, AM, PAM, etc. here)? My response always is…it depends. Yes, I know I am dodging the question, but arguably, it is impossible for […]
