The Next IGA Revolution: How IGA is Going to Change in 2026 to Scale Faster and Easier

You may be looking at your 2026 budget and trying to plan your Identity Governance and Administration (IGA) priorities. If you’re a few years into your IGA deployment, you may be finding it increasingly challenging to keep attention and executive support, while still facing a large backlog of applications that are not covered. Or, you […]
My Agentic Journey: The journey to seamless, secure AI / Identity integration
Over the last 3-6 months, I’ve had a ton of conversations around Secrets and Non-Human Identities (NHI), governance, authentication, and authorization with many of them leading to the inevitable AI overlay of the same topic. Now, I say it that way because we’re getting more mature when it comes to building and securing interactive and […]
Simplifying the Complex for Dynamic Authorization: Just ask the question to get a response

As we go into 2025, I’ve seen a number of different articles and posts around what is going to be critical this year in IAM. I think a lot of what I have been seeing and consensus has been Non-Human Identity, passwordless / adaptive authentication, identity verification, and (interestingly) dynamic authorization. I could see everything […]
IAM Program Red Flags and Path Forward

When starting an evaluation of an IAM program, what are some of the common red flags I look for in evaluating the maturity and strength of the IAM capability. See some common pitfalls and solutions to address these common red flags.
Improving IGA Visibility Through New and Modern Tools and Methods

See how changing definition of connected and new tools and methods are helping improve success of IGA deployments
Founders Update – From the CIdO
How do we start rethinking IAM and how it can be better utilized in our organizations. This is my call to arms and why. See why the CIdO, why now, and how we rethink IAM.
IAM Implementations and the Sacred Timeline
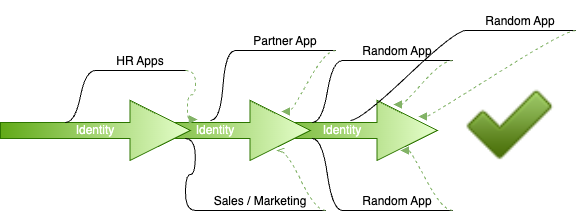
How do we realign moving targets into our IAM program without interrupting business? See how you can achieve success purging individual branches back into the IAM timeline.
Identity First Modeling

How do we move Identity beyond just a security tool. Read more to see Identity First vs Identity First Security.
Attesting to Whats Not There: The shifting paradigm of audit and compliance with ZSP / JIT PAM

How do we audit accounts and privileges when they are assigned as needed? This discusses the shifting audit and compliance requirements with ZSP/JIT and PAM.
History Repeats Itself – My View of the CrowdStrike Incident
There has been a ton of commentary, analysis, and responses regarding the CrowdStrike incident that happened on July 19, 2024. As of today, July 26, 2024 there are still companies recovering and trying to get back to normal operation. In the coming months, I’m sure there are going to be hearings and other outcomes related […]
